Don't worry about the suspicious files which the
.sys.mui ones we feel are due to an overly sensitive heuristics, seeing the double file extension; an old trick used to try and hide what the true file extension/purpose is.
The C:\Windows\System32\drivers\wimmount.sys we suspect is a false positive.
####
I think there is definitely something there but probably not an MBR Rootkit as aswMBR is reporting a Windows 7 default MBR code. But it is showing an Unknown hook. So this may be a TDL rootkit.
However, you may want wait for instructions form essexboy on how to proceed.
I think Essxeboy may well recommend that you run TDSSKiller to see if that can deal with it, but he may not be back on-line until tomorrow evening as it is now 11:57pm in the UK and he has to be up for work tomorrow.
~~~~
I leave the choice up to you if you wish to wait:
Please read carefully and follow these steps.
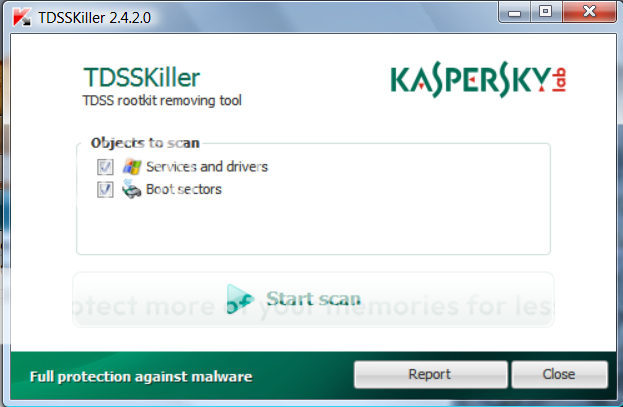
- Download TDSSKiller and save it to your Desktop.
- Extract its contents to your desktop.
- Once extracted, open the TDSSKiller folder and doubleclick on TDSSKiller.exe to run the application, then on Start Scan.
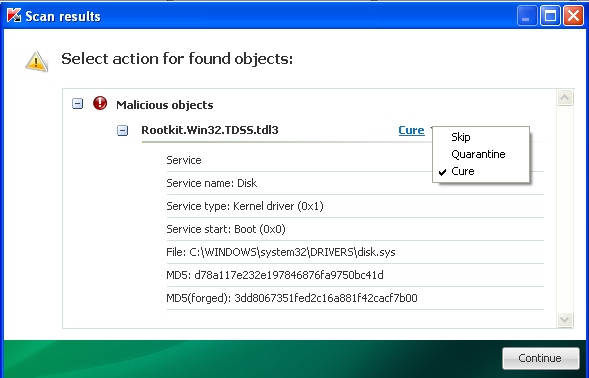
- If an infected file is detected, the default action will be Cure, click on Continue.
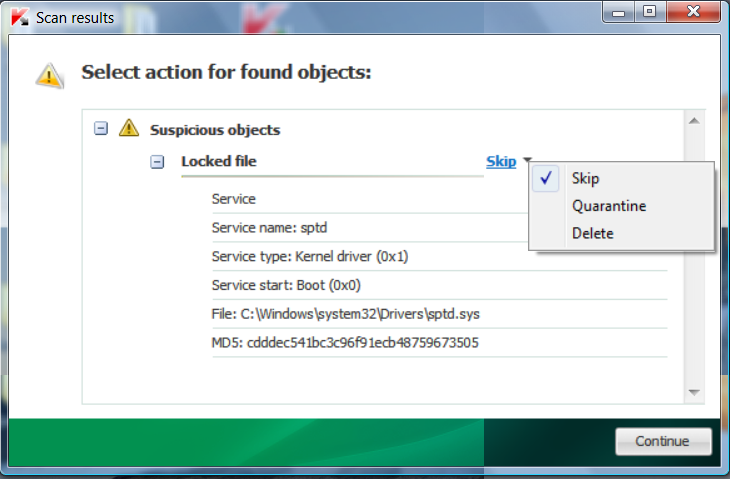
- If a suspicious file is detected, the default action will be Skip, click on Continue.
- It may ask you to reboot the computer to complete the process. Click on Reboot Now.
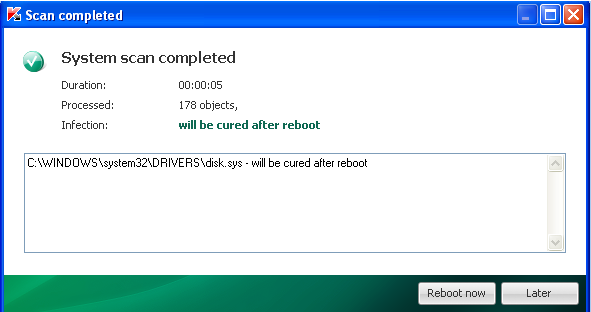
- If no reboot is require, click on Report. A log file should appear. Please copy and paste the contents of that file here.
- If a reboot is required, the report can also be found in your root directory, (usually C:\ folder) in the form of "TDSSKiller.[Version]_[Date]_[Time]_log.txt". Please copy and paste the contents of that file here.